Note
This article has been updated for 2023.
When choosing a password, most people don’t place much of an importance on the complexity or uniqueness of the password to ensure it’s secure. Unfortunately, hackers out there are continually scanning and attempting to remotely exploit your passwords to all of your accounts.
The damage and devastation they can cause can be significant, especially if they gain access to things such as your online banking, your business website or even all the files on your PC.
Think of it like your home or car, how often do you leave your door unlocked or use a very simple latch? It’d make it a great target for thieves to exploit since they don’t have to worry about breaking in. The same problem exists with computer passwords, hackers continually look for and try very weak passwords as an easy method of access.
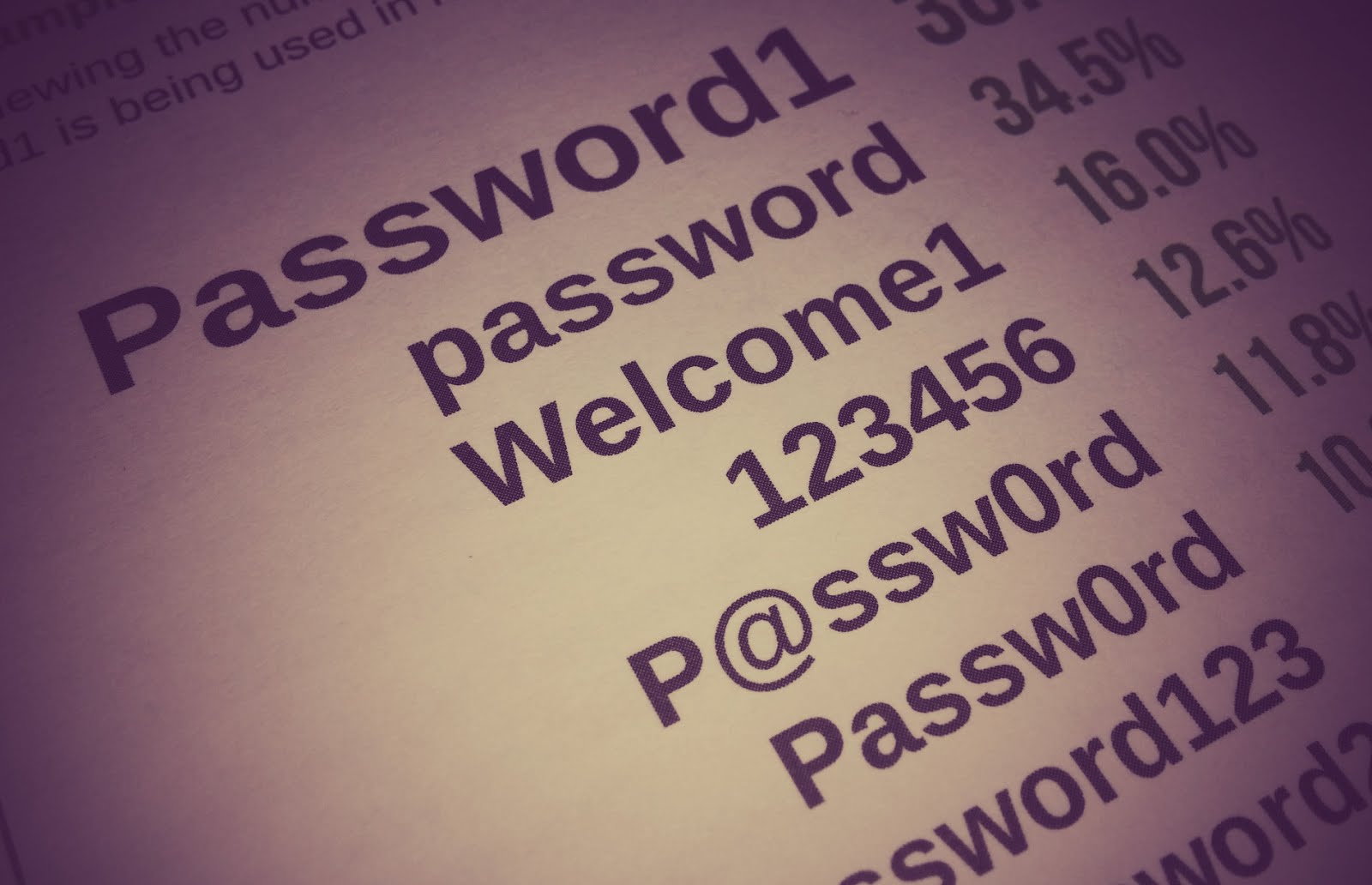
Hackers use what’s called “dictionary attacks”, meaning they have a database of the most commonly used passwords in which they attempt to gain access with. Even those who think they have obfuscated their password by using something such as “Pa@ssW0rd” are very vulnerable to attack. Even worse, something as simple as “Password1” or “12345678” has been used by hundreds of thousands of others and therefore one of the most easily hacked. They then combine it with typically used English words as well as combinations of your username to attempt to brute force your passsword.
A previous study by TrustWave (one of the world leaders for online security) found that in a database of 3.1 million compromised passwords, only 33% were unique. That means on average, two out of the three passwords you’ve used have also been used by someone else. Would you feel safe knowing that your car or house keys were exactly the same as others? I know I certainly wouldn’t!
Once a hacker has gained access to a system such as your email account, they can then do things such as request password resets for systems such as Facebook, eBay, PayPal, Dropbox and many, many other systems. If you have all of your emails online, it also means that they’re able to read all of your emails. This information could then be used for identity theft to commit credit card fraud or used to further exploit and trick other people. It’s not a nice situation to find yourself in, that’s for sure.
How to ensure your passwords are secure
Now that you know why you need to secure your password, the next question is how. Here’s a quick checklist to reference:
Use a complex password
The easier the password is, the easier it is to crack or guess. The most effective way to prevent this is ensuring that your password isn’t based on something that’s easy to guess or generate. A basic 6 character password (no matter how complex) can be cracked in less than one minute with modern computing power.
Here’s a checklist:
- Don’t use dictionary words, or passwords that contain your username, personal name or business name
- Ensure that the password is at least 12 characters long
- Optionally, include at least one uppercase character, one non-alphanumeric character (eg !@#%^&*) and at least one numeric character
The key message here is the password length.
Go for a longer password as the length significantly contributes to how hard this is to crack. XKCD have a great comic based on this very scenario:

Update (2020): In recent years as compute power evolves and the ability to get cheap compute power via the cloud has taken off, even passwords with 8 characters with complex, non-alphanumeric characters can be brute forced within hours.
There are various online tools to help you generate secure passwords, here’s a few we recommend:
Test the Complexity
You can also check your password complexity to see how secure it is. These tools use client side JavaScript to test the complexity, so the password isn’t uploaded to any server. We still recommend that you don’t ever type your password into any form which isn’t the correct one. However, you can use a similar pattern to test the complexity. This will then give you an idea how secure your passwords are. Here’s the tools:
Never use the same password twice
Regardless of how complex the password is, the moment it’s compromised (meaning someone has access to it) it means hackers have access to all of your other accounts. For example, if you set the same password for your Facebook account and your online banking, any security problem with Facebook would mean hackers could access your online banking.
Keep your passwords in a safe place
Treat your passwords just the same as you do your office or house key. Don’t store your passwords in a word document or text file on your computer. Never leave them laying about in your office or home, someone may copy them without you even knowing!
The best place to store your passwords is with a good password management system. These include (but not limited to):
If you don’t want to use a password manager, as a last resort the next safest place is in hardcopy (ie, not on your PC) and stored in a safe.
Check your account for previous exploits
The best service for this is have i been pwned?. This is a database of exploited login details with millions of accounts listed and run by an Australian security expert, Troy Hunt. Have i been pwned allows you to put your email address in and it will show you what sites you’ve had a login with where they’ve experienced a compromise and therefore that password could be also compromised.

It’s generally a stark reminder why using unique passwords are so critical. If you’ve used a common password with any of the sites listed, then it’s possible that hackers can use this to login to any of the other sites, banks or systems where you’ve got the same password.
Further security measures
Having a secure password is a good start, but you can take it further than this. Where possible, use Multi Factor Authentication (MFA). This means that not only do you need to use a password, but you also need verification from a secondary system. This could be a code via an SMS message, an App on your phone like the Google Authenticator or a physical key such as the YubiKey.

Having two-factor authentication in place ensures that even if your password has been compromised, you’re still protected through this secondary authentication method. Even if a hacker was able to get a copy of your password, they need the secondary authentication to be able to proceed. There’s no easy way for them to bypass this, which is what makes the two-factor system much more secure.
Conclusion
By ensuring you’re using secure passwords, you protect one of the most commonly exploited methods of gaining information or access to your systems. Hackers are always looking at ways of improving their efficiency of attacks, so it’s important to stay vigilant.
We also recommend that you investigate the use of a password manager (such as BitWarden, LastPass, 1Password or KeePass) as well as two-factor authentication for any critical systems. Conetix has MFA enabled and available both for billing as well as any VPS servers to keep you secure. You can view a list of which platforms support MFA here: https://twofactorauth.org/.
Lastly, always ensure that your anti-virus and anti-malware systems are up-to-date. If a keylogger is installed on your system, then your password will be compromised no matter how complex it is.


